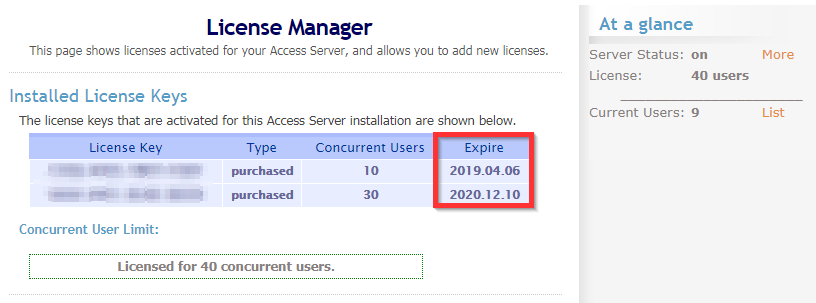
Keenetic-3.key - private key of the 2nd OpenVPN client (Keenetic-3) ta.key - HMAC key for additional protection against DoS-attacks and flooding The only thing left to do is to add their contents to the server and client configuration text files. If you continue using your current OpenVPN Access Server as it is without either upgrading or applying the licensing patch, it will function normally and the license keys that are on it right now will continue working just fine, even after January 20th (assuming your license keys do not expire before then of course). Once you click Go button, you should be able to get the OpenVPN Access Server in the result. Click the OpenVPN Access Server title to proceed. It will give you more details about the OpenVPN Access Server. Select the region you would like to launch the OpenVPN Access Server instance and click Continue button. In this demonstration, I have.
In this HOWTO, I have demostrated how to deploy a OpenVPN server on AWS, and how to connect your AWS resources from end user devices through OpenVPN client program.
What is OpenVPN Server ?
OpenVPN is an open-source software application that implements virtual private network (VPN) techniques for creating secure point-to-point or site-to-site connections in routed or bridged configurations and remote access facilities. It uses a custom security protocol that utilizes SSL/TLS for key exchange.
Openvpn Access Server License Key Not Working

AWS provides this OpenVPN server as an AMI to provide secured point-to-point connection between your AWS site to your site situated anywhere in the world. This will be helpful for mobile users want to connect your company AWS resources in a secure way.
So, this HOWTO explains how to setup a Software Defined Private Network in AWS cloud environment, and how a client can connect his AWS resources through OpenVPN server.
8 Steps total
Step 1: Preparing your Environment
What are all the components involved in this preparation -
OpenVPN Access Server Appliance [In the form of : AMI]
OpenVPN Client Software
VPC Configuration hosted at AWS
Licensing :
OpenVPN Access Server licensing comes pre-bundled with your Amazon EC2 instance providing the flexibility of hourly billing with no upfront costs or long-term investments i.e in one word : Pay As You Go.
Let’s assume that you already have a basic hands-on experience in AWS cloud services like hosting VPC and launching instances. Below diagram shows clearly how a remote user connected to AWS private network using Open VPN Gateway client through a secured VPN tunnel.
Step 2: Launching Open VPN Server Appliance

On our first step, we are launching Open VPN Server Appliance from AWS Market place. Note that, Open VPN Server instance will be charged as per the no of concurrent connection license it has. You can choose any Open VPN server appliance as per your need.
First login to AWS Market Place with a valid AWS console login.
https://aws.amazon.com/marketplace/
Enter OpenVPN Access Server in the search window, and press Enter.
Step 3: Launching Open VPN Server Appliance - Step 2
Search result will shows available Open VPN Server instances with various connection count. Please note that, depends on connection count and Region of deployment your monthly bill will vary.
Select any one of the Open VPN Server appliance for deployment.
Step 4: Launching Open VPN Server Appliance - Step 3
Click continue to launch the instance. For a simple launch process, choose “1-Click Launch” option and proceed with default option, However user can always have flexibility to make fine adjustments like Changing AWS “Region”,EC2 Instance Type, VPC Settings and security group information.
While launching the Server Appliance, you will be noted to create a new key pair to connect the instance. Create a new pair and keep it safely to connect the instance later.
Click “Launch with 1 click” button after you have confirmed all of the selected options are correct.
To confirm that the instance has successfully launched, watch the Instances section for status. You should see something similar to the following as your instance is being launched. Once you see 'Instant status' is running, your Open VPN Server Appliance is ready for configuration.
Step 5: Assigning an Elastic IP to the Instance
Though its option, you should allocate a static IP address for your appliance so the IP address can be reclaimed in case of AWS machine failure/shutdown/reboot. To do so, visit the Elastic IPs section in the left navigation panel.
Step 6: Configuring OpenVPN Access Server Instance
Once your new instance is successfully launched and running, you will need to SSH into the console using a SSH client software and the private key pair you have used/created previously.
When login screen is prompted, use openvpnas as the username, and then press Enter. (NOTE: If you are using previous versions of our appliance, the username used is root instead of openvpnas)
If the private key you have specified was correct, you should now be logged in and the OpenVPN Access Server Setup Wizard should now be started. Follow the instructions below to begin configuring your server.
Read through the EULA, and enter yes to indicate your agreement acceptance.
>> Will this be the primary Access Server node?
Default: Yes, Press Enter to accept the default setting. Otherwise, if you are setting up your failover node, change this to say no. Here we are setting up primary Access Server node. So default selected.
>> Please specify the network interface and IP address to be used by the Admin Web UI:
Default : 2, Choose 1 – “all interfaces: 0.0.0.0” to listen in all interface.
>> Please specify the port number for the Admin Web UI.
Default: 943, It is usually safe to leave this at the default port unless customization is desired.
>> Please specify the TCP port number for the OpenVPN Daemon
Default: 443, It is usually safe to leave this at the default port unless customization is desired.
>> Should client traffic be routed by default through the VPN?
Default: No, If you only have a small network you would like your remote users to connect over the VPN, select no. Otherwise, if you would like everything to go through the VPN while the user is connected (especially useful if you want to secure data communications over an insecure link), select yes for this option.
>> Should client DNS traffic be routed by default through the VPN?
Default: no, If you would like your VPN clients to able to resolve local domain names using an on-site DNS server, select yes for this option. Otherwise, select no. Do note that if you selected yes for the previous option, all traffic will be routed over the VPN regardless what you set for this setting here.
>> Use local authentication via internal DB?
Default: yes, If you would like OpenVPN Access Server to keep an internal authentication database for authenticating your users, select yes for this option. When this option is turned on, you will be able to define and/or change username and passwords within the Admin Web UI.
>> Should private subnets be accessible to clients by default?
Default: yes, This option defines the default security setting of your OpenVPN Access Server. When Should client traffic be routed by default through the VPN.
>> Do you wish to login to the Admin UI as “openvpn”?
Default: Yes, This defines the initial username in which you would use to login to the Access Server Admin UI area. This username will also serve as your “lock out” administrator username shall you ever lock yourself out of your own server. If you would like to specify your own username, select no. Otherwise, accept yes for the default.
> > Please specify your OpenVPN-AS license key (or leave blank to specify later):
Explanation: If you have purchased a license key for your OpenVPN Access Server software, enter it here. Otherwise, leave it blank. OpenVPN Access Server includes two free licenses for testing purpose.
>> Create password for the OpenVPN admin user, invoking the below command.
sudo passwd openvpn
Enter new UNIX password:
Retype new UNIX password:
Last thing we need to do before we can connect to the admin area and to our VPN is disable the Source/Destination check in AWS. Without doing this we would not be able to access our private subnets.
Openvpn Access Server License Key
To change this go to the EC2 console in AWS, select your instance, choose *Actions>Networking>Change Source/Dest. Check* as seen below. Choose “Yes, Disable” on the next screen.
Step 7: Testing OpenVPN server connectivity
Here, we are setting up a test instance on the same private subnet VPC where the OpenVPN server exist.
1.Login to your AWS account and navigate to the EC2 Dashboard and click “Launch Instance” on the left.
Press “Select” next to the top item *Amazon Linux AMI*
2. Leave on t2.micro and click “Next: Configure Instance Details.”
3. Make sure to set your subnet into your private subnet mentioned in the prerequisites. Then click “Review and Launch” as defaults for everything else are fine for this test.
Step 8: Connecting AWS instance from the client
Install the OpenVPN client on end user machine and connect to the instance running in the private subnet on AWS.
In your web browser enter the Elastic IP from your OpenVPN Access Server https://elastic-ip-here:943 Note: On your first attempt to connect you will be warned by your browser that the SSL certificate cannot be validated. This is OK for our demo but in a real world you will want to setup a real SSL certificate in your setup.
On the screen enter “openvpn” for the Username and the password you created for the user.
After your credentials are accepted you will see the screen below. Go ahead and click “Click here to continue” which will download the OpenVPN client installer to your machine.
Thus, Open VPN Server appliance is deployed on our AWS account, and you can create as many AMIs on that created VPC. Now authenticated users can login to connect their AWS AMIs securely through the installed VPN Client.
Deploying a Open VPN server providing an extra security for the end users, and it is easy to deploy a OpenVPN server on your AWS account.
References
- Vembu Blog
4 Comments
- AnaheimWRXDriver414 Jun 22, 2017 at 06:52pm
Any steps to setup LDAP auth in a windows domain environment by chance?
- Pimientoselvarajmanoharan Jul 24, 2017 at 02:49pm
Hi,
Can you please clear about your question ? You want to know LDAP auth for functionality in windows? or AWS auth with LDAP Protocol ? - Anaheimreeceline Feb 6, 2018 at 08:05pm
Great guide, easy to follow was able to setup OpenVPN.
- Pimientomhghg-2020 Apr 25, 2020 at 06:57am
Can you show us how to set up openvpn server on ubuntu Server 20.04 LTS if possible please?
We will see here how to set up a OpenVPN server under MicrosoftWindowsServer.
OpenVPN is a very powerfull VPN which has several advantages : it is free, compatible with most operating systems, easy to implement and highly configurable.
Network diagram
Server configuration
- OpenVPN Server :
- OS : Windows Server 2016
- Role : OpenVPN Server
- IP : 192.168.0.200
Installing OpenVPN
Go to OpenVPN official website and download https://openvpn.net/ last installer.
- As we want to install OpenVPN as server we will choose Customize :
- We enable OpenVPN Service in order to make it work at boot :
- And we install EasyRsa in order to be able to create server and clients certificates :
- Once done click Close :
Setting up Certificate Authority (CA) and generating certificates and keys for server and clients
Here we will set up a pki to be able to create our server and clientscertificates.
- Open a Command Prompt as administrator :
- And type the following commands to enter inside EasyRSA shell :
- Remove existing configuration, just for good measure :
- Initialize pki, and type yes to confirm :
- Build certificate authority :
- Build server certificate and key :
- Generate Diffie Hellman parameters :

- Generating client certificates :
Certificates
- Put this files (from C:Program FilesOpenVPNeasy-rsapki, C:Program FilesOpenVPNeasy-rsapkiissued and C:Program FilesOpenVPNeasy-rsapkiprivate) :
- ca.crt
- dh.pem
- server.crt
- server.key
- To C:Program FilesOpenVPNconfig-auto and C:Program FilesOpenVPNconfig folders.
Add a Windows Firewall Rule
We need to open 1194udp port to allow OpenVPN clients connections. Use the Windows Firewall Management Console or this command inside a Administrator command line console to do that.
C:Program FilesOpenVPNconfig-autoserver.ovpn
As administrator, edit C:Program FilesOpenVPNconfig-autoserver.ovpn file :
Then, restart the OpenVPN service :
- From, services management console :
- Right click OpenVPNService then Restart :
- Or from an administrator Command Prompt :
Client configuration
- OpenVPN Client :
- OS : Windows 10
- Role : OpenVPN Client
Installing OpenVPN
We will download the same package, and here install with default parameters.
Copy certificates from the Server
- From the Server get the following files (from C:Program FilesOpenVPNeasy-rsapki, C:Program FilesOpenVPNeasy-rsapkiissued and C:Program FilesOpenVPNeasy-rsapkiprivate) :
- ca.crt
- client01.crt
- client01.key
- And paste them to C:Program FilesOpenVPNconfig.
- C:Program FilesOpenVPNconfigclient.ovpn
Edit the client.ovpn file with administrator rights :
Establishing the connection
- Run as administrator
- Start the connection
- A pop up will confim that we are connected
Server Access
To join the server we will use the 10.50.8.1 IP Address
Troubleshooting : After a Windows Update, I couldn't have access to the server share anymore (OpenVPN was able to connect though). To make it work again, I had to repair the OpenVPN program on the server side.